Tag: oauth
-

When one login method is not enough
In the first version of this case, I deliberately kept things focused. The goal was to prove that a user could come in through Google, complete a minimal onboarding flow, receive ORDS client credentials, and actually use those credentials against a protected endpoint. That loop, once it closes, already carries a lot of value, and
-
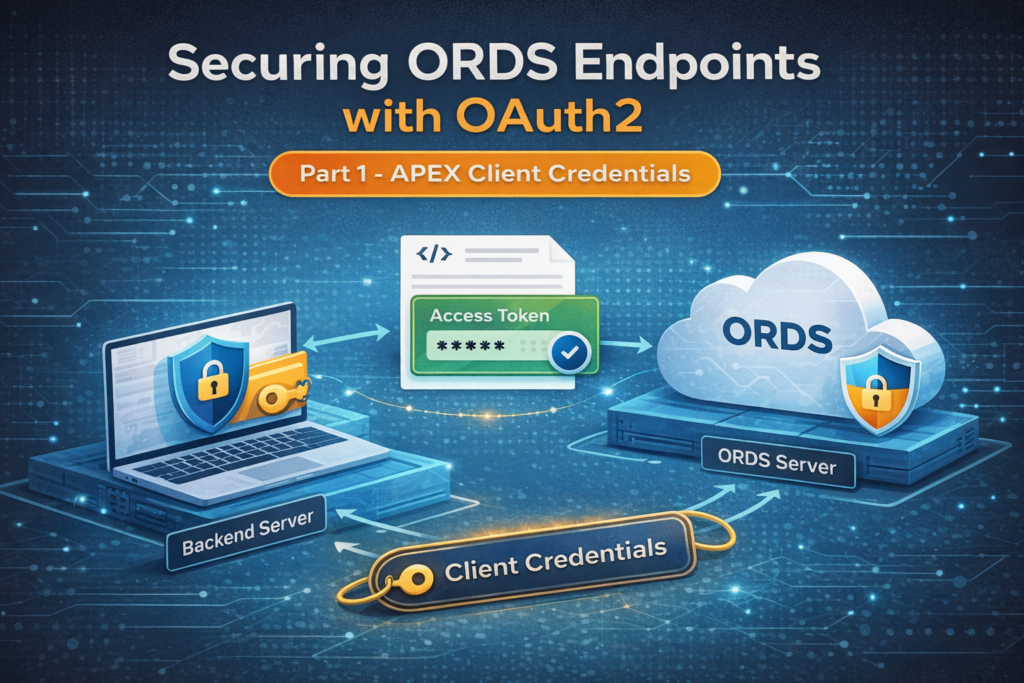
Securing ORDS Endpoints with OAuth2
In this article, I demonstrate how to secure ORDS REST endpoints using OAuth2 Client Credentials within Oracle APEX running on Autonomous Database (OCI). The post walks through creating roles and privileges via the APEX RESTful Services interface, configuring an OAuth client using SQL Workshop, and validating the full authentication flow using Postman. This example highlights…